The umask (User Mask) command in Linux is a built-in shell command which sets the default file permissions for newly created files and directories.
In this tutorial, we will learn about the umask command and how to use it to define default file permissions.
What is umask?
umask stands for "user file creation mask", which defines the default permission set when a new file or directory is created. Permissions in Linux are based on a three-group system:
- User: Defines owner permissions. The user who creates the file or folder is the default owner.
- Group: Defines group permissions for a Linux group that share the same permissions for a file or directory.
- Other: Defines permissions for anyone who is not the owner and is not part of the group. When these permissions are set, anyone can access the files and folders. We generally call them world-readable files and directories.
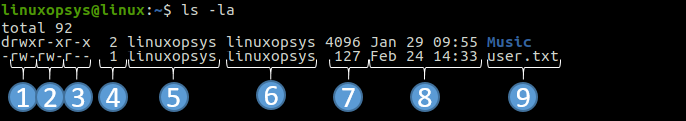
Each group can have permissions for read (r), write (w), and execute (x). These permissions correspond to numerical values:
- Read (r): 4
- Write (w): 2
- Execute (x): 1
The umask command manipulates these permissions by "masking" bits out of the system's default permission setting.
umask Command
As mentioned before in the introduction, the umask command is used to set the default umask value for files and folders in Linux. All the newly created files and directories on your system will use the permissions defined by the umask command.
Use the umask command without any options to check the current mask:
umask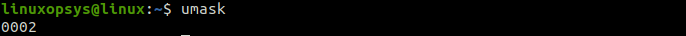
0002 means that the first digit 0 is known as a sticky bit, which is a special security feature. The next three digits denote the octal umask value of the file or directory umask.
Syntax
The basic syntax of the umask command:
umask [-p] [-S] [mask]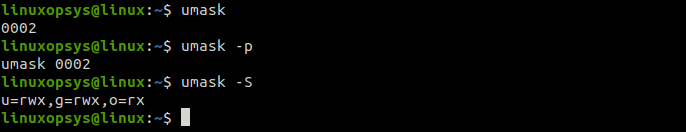
Options
You can use the following options with umask:
- None : Set the umask value (when accompanied by an octal).
- None : Display the current umask value in octal format.
- -p : Output in a format that can be reused as input.
- -S : Display the current umask in a symbolic format.
Umask Value
The umask value is represented in both symbolic and numeric formats.
The symbolic format is represented in the rwx (read-write-execute) format. The leftmost character is for read permissions, the middle character is for write permission, and the rightmost character is for execute permission. For example, if symbolic umask is set to r-- for the owner, then the owner will have only the read permissions on the particular file or directory.
The octal mode umask values are described in the following table:
| Permission | Octal Value | Binary Value | Description |
|---|---|---|---|
| - | 0 | 000 | No permission |
| -x | 1 | 001 | Only execute permissions |
| -w- | 2 | 010 | Only write permission |
| -wx | 3 | 011 | Write and execute permissions |
| r- | 4 | 100 | Only read permissions |
| r-x | 5 | 101 | Read and execute permissions |
| rw- | 6 | 110 | Read and write permissions |
| rwx | 7 | 111 | All permissions- read, write, and execute |
Umask Value for Files and Directories
Before changing the umask value on your system, you must understand its impact on the default file and folder permissions.
The default system permission for files is 666 (rw-rw-rw-) and for directories is 777 (rwxrwxrwx).
The default mask value is 002. It changes folder permissions to 777-002 = 775 (rwxrwxr-x) and file permissions to 666-002 = 664 (rw-rw-r--).
The final umask value results by subtracting the default mask value from the default system values (777 and 666).
Setting the Umask Values
It's good, we explain with examples.
To set folder permissions for owner, group, and others to read, we need to set umask to 333:
umask 0333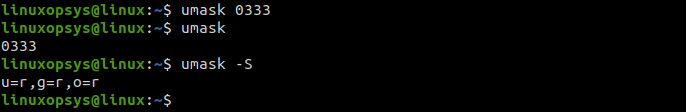
You can also use symbolic values to set umask:
umask u=rwx,g=rwx,o=r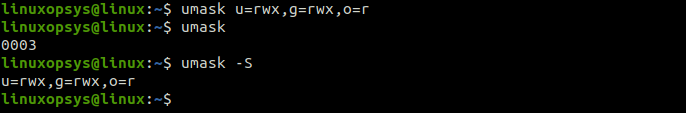
Where:
u sets permission for the user/owner.
g sets permission for the group.
o sets permissions for others.
The command only sets the specified file permissions. For example, for others we want to assign only read permissions, so we specify a symbolic value of only read (r).
To make the umask setting persistent across sessions edit appropriate profile scripts such as ~/.bashrc or /etc/bash.bashrc file.
Difference between umask and chmod
The umask command and chmod commands are both used to set permissions in Linux, but they are inherently different from each other.
The umask command changes the default permissions and thus the permissions set using this command are automatically applied to all the newly created files and directories.
The chmod command changes permissions for the existing files and folders. For example, if you assign ownership of the file named services to user tom and group adm, then the change will be limited to services file only. It will not affect any other file on your system.
The umask command affects permissions for the entire system, whereas the chmod command affects permissions of only the specified files.

Comments